Building AI-Native Cyber Defense: A Practical Guide to Leveraging Frontier AI
Overview
The rapid evolution of frontier artificial intelligence—pioneered by labs like OpenAI, Anthropic, and Google DeepMind—is reshaping the cybersecurity landscape. While attackers gain speed and scale in discovering vulnerabilities, defenders can harness the same advances to build autonomous, AI-native defense systems. This tutorial walks you through the principles and practical steps to implement a modern cyber defense approach inspired by SentinelOne’s proven strategy: operating at machine speed with behavioral AI, automation, and platform-wide protection.
By the end, you'll understand how to integrate frontier models, deploy autonomous response, and avoid common mistakes that reduce the gap between theoretical risk and operational security.
Prerequisites
- Basic knowledge of cybersecurity concepts (threats, vulnerabilities, zero-day exploits)
- Familiarity with AI/ML fundamentals (behavioral models, anomaly detection)
- Access to a security operations platform or API that supports AI integration (e.g., SentinelOne, custom stack)
- Administrative privileges on endpoints, cloud environments, and network devices for deploying agents
- Understanding of supply chain risk and trusted workflows
Step-by-Step Instructions
Step 1: Assess Your Current Defense Posture
Before integrating frontier AI, evaluate your existing security controls. Identify gaps where manual processes slow response—especially for zero-day vulnerabilities and novel attacks. Note the attack surfaces you protect: endpoints, cloud workloads, identities, data, networks, and AI pipelines.
Example: A typical enterprise may rely on signature-based antivirus and manual patching. These fail against unpatched exploits like those in the LiteLLM or Axios supply chain attacks. Document these weak points.
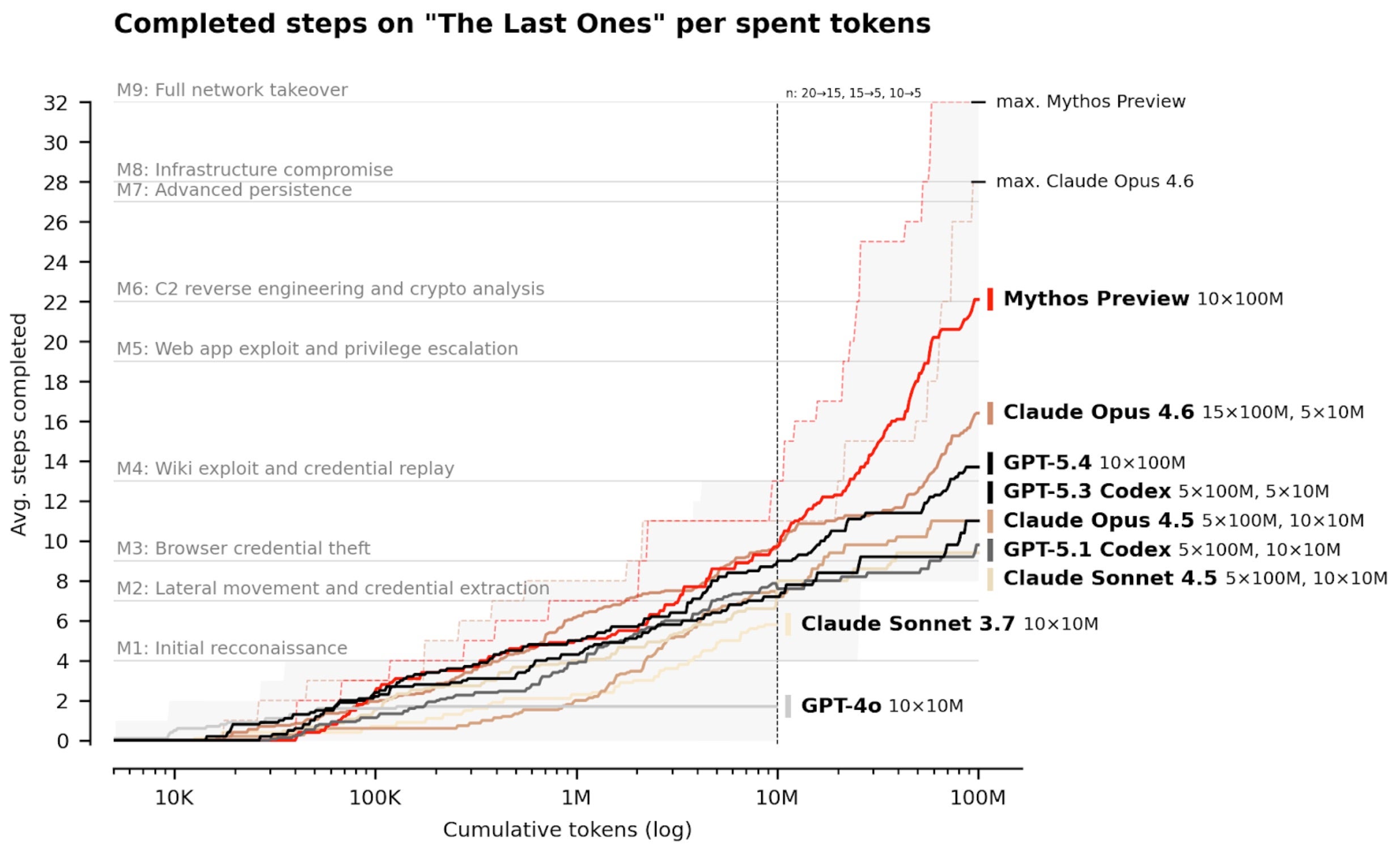
Step 2: Understand Frontier Model Capabilities
Frontier AI models excel at reasoning about attack paths, analyzing complex systems, and identifying weaknesses at scale. However, raw vulnerability counts do not equal real-world risk. Many discovered bugs are not exploitable in live environments due to architectural layers, controls, and runtime protections.
Key insight: Use frontier models to prioritize vulnerabilities based on actual exploitation likelihood, not just CVSS scores. This is where behavioral AI adds value—it understands real conditions.
Step 3: Deploy Behavioral AI Across All Surfaces
Behavioral AI models learn normal patterns across endpoints, cloud, identity, data, and network. Deploy agents on each surface with lightweight ML inference capabilities. The model continuously updates its baseline by observing user, process, and network behaviors.
Pseudo-configuration example:
{
"agent": {
"type": "behavioral-ai",
"surfaces": ["endpoint", "cloud", "identity", "network", "data", "ai-pipeline"],
"model": "frontier-v2",
"update_frequency": "continuous",
"anomaly_threshold": 0.95
}
}Integrate with your SIEM or SOAR to feed behavioral signals into a central reasoning engine.
Step 4: Integrate Frontier AI Models for Advanced Reasoning
Connect your behavioral AI outputs to frontier models from labs like OpenAI, Anthropic, or Google DeepMind. Use their reasoning abilities to correlate anomalies, trace attack paths, and suggest autonomous responses. These models should run in a sandboxed environment with data privacy controls.
API integration example (Python-like pseudocode):
import frontier_api
def analyze_alert(anomaly_data):
prompt = f"Analyze this behavioral anomaly: {anomaly_data}. Is it a zero-day exploit? Recommend an autonomous response."
response = frontier_api.complete(prompt, model="claude-3-opus")
return response.decisionStep 5: Implement Autonomous Response at Machine Speed
Based on the frontier model’s recommendations, automate response actions—blocking processes, isolating endpoints, revoking identities, or terminating cloud instances. The response must occur faster than any human analyst could manually intervene. This is critical for supply chain attacks like CPU-Z, where the window for blocking is minutes.
Automation workflow:
- Behavioral AI detects anomaly (e.g., abnormal process spawning).
- Frontier model classifies as zero-day exploit.
- Automated playbook executes: kill process, block network connection, alert SOC.
- Machine-speed response completes in under 5 seconds.
Step 6: Monitor, Iterate, and Collaborate
Continuous improvement is vital. Analyze telemetry from autonomous responses to refine models. Collaborate with frontier labs and the security community to share insights (within confidentiality bounds). SentinelOne’s partnerships with labs provide early access to model updates and threat intelligence.
Metrics to track: time-to-detection, time-to-response, false positive rate, number of zero-days blocked.
Common Mistakes
Mistake 1: Over-Reliance on Vulnerability Counts
Many teams focus on patching every disclosed CVE. However, as the original text notes, raw vulnerability counts rarely map to real-world risk. Fix: Prioritize vulnerabilities that are actively exploited or likely to bypass runtime protections. Use frontier AI to assess operational exploitability, not just theoretical severity.
Mistake 2: Ignoring Runtime Protections
Architectural layers, controls, and mitigations can reduce the impact of many vulnerabilities. Failing to deploy runtime defenses (e.g., behavioral blocking, application control) leaves you exposed even after patching. Tip: Combine preventive measures with autonomous detection and response.
Mistake 3: Manual Response Delays
Relying on human analysts to respond to every alert is too slow for modern attacks like supply chain compromises. Solution: Automate response at machine speed—only escalate to humans for complex decision-making.
Mistake 4: Treating AI as a Black Box
Using frontier models without understanding their reasoning can lead to false confidence. Best practice: Keep a human-in-the-loop for critical decisions and continuously validate model outputs against ground truth.
Summary
Implementing AI-native cyber defense requires shifting from signature-based, manual responses to autonomous, behavior-driven systems powered by frontier AI. By following the steps—assessment, deployment of behavioral AI, integration with frontier models, automation at machine speed, and continuous iteration—you can defend against advanced threats like zero-day exploits and supply chain attacks (e.g., LiteLLM, Axios, CPU-Z). Avoid common pitfalls such as over-prioritizing vulnerability counts, neglecting runtime protections, delaying response, and treating AI opaquely. The result is a security posture that stays ahead of attackers, leveraging the same frontier advances that empower adversaries.
Related Articles
- NHS England's Open-Source Software Withdrawal Sparks Debate on Security vs. Openness
- 5 Critical Facts About the .NET 10.0.7 Out-of-Band Security Patch
- Critical Rust Package Manager Vulnerability Allows File Permission Manipulation
- Securing the npm Ecosystem: Evolving Attack Vectors and Defensive Strategies
- Linux Kernel Patches Land in Urgent Security Update for Dirty Frag Vulnerability
- Machine-Speed Defense: How Automation and AI Reshape Cybersecurity Execution
- Zero-Day Supply Chain Attacks Surge: SentinelOne Blocks Three Unseen Payloads in Single Day
- Cisco Acquires Astrix Security to Fortify AI Agent Defenses in Production